In-Person Meetings,
Made to be Memorable
Create a seamless event experience with our onsite event technology solutions designed to increase attendee engagement, deliver valuable metrics, and give your attendees and partners peace of mind.

Industry-Leading Onsite Solutions that Enhance
the Attendee Journey
Streamline Registration
Deliver seamless check-in with Stova’s customizable registration solutions, no matter the event size. Reduce wait times and delight your attendees as soon as they walk in the doors.
Establish Connections
With Stova’s custom mobile app solutions, build connections between attendees and exhibitors powered by AI and machine learning technologies.
Deliver Data
The valuable attendee data captured can be seamlessly shared between your CRM and registration software, allowing you to focus on what matters most – your event, not manual workarounds.
Delight Sponsors
Sponsors and exhibitors analyze attendee data in real-time with powerful lead capture tools on Stova’s mobile app, giving them the ability to qualify and make notes as meetings happen
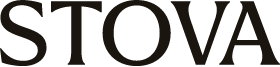
Deliver Bespoke Badging & Check-In
Our broad array of options allows for onsite event technology solutions that are either customized to your needs or out-of-the-box. No matter your budget or event size, our event ecosystem offers a product for every unique need.
Deliver Smooth Registration
Stova’s onsite hardware options include mobile check-in carts, tablets, mobile devices, laptops, and NFC hot spots.
Customize Badging Seamlessly
Badges can be plastic or paper card stock, and can be scanned via NFC, QR, BLE, or UHF technology, offering a solution for every event.
Bespoke or DIY Badging & Check-In
From tier 1 events to small and mid-size events, Stova has you covered. Discover BadgeNext -- simplify check-in and enhance attendee satisfaction with this out-of-the-box technology.

Turn Any Area into a Check-in Station
Create a safe and positive first impression for your attendees as soon as they step onsite with our fully integrated, contactless, easy-to-use check-in and badging solutions along with other onsite technology solutions.
Enhance the Attendee Journey
Cut down long lines and wait times at your main registration area by giving attendees the option to check themselves in at designated remote check-in locations.
Give Attendees Registration Power
Portable check-in carts can be set up anywhere from airports to hotel lobbies, allowing your attendees to get checked-in and retrieve their badges immediately.
Integrate Easily
All remote check-in options are fully integrated with Stova Registration, meaning that badges will always reflect the most recent, accurate information. Check-in can also integrate easily with any other registration provider!


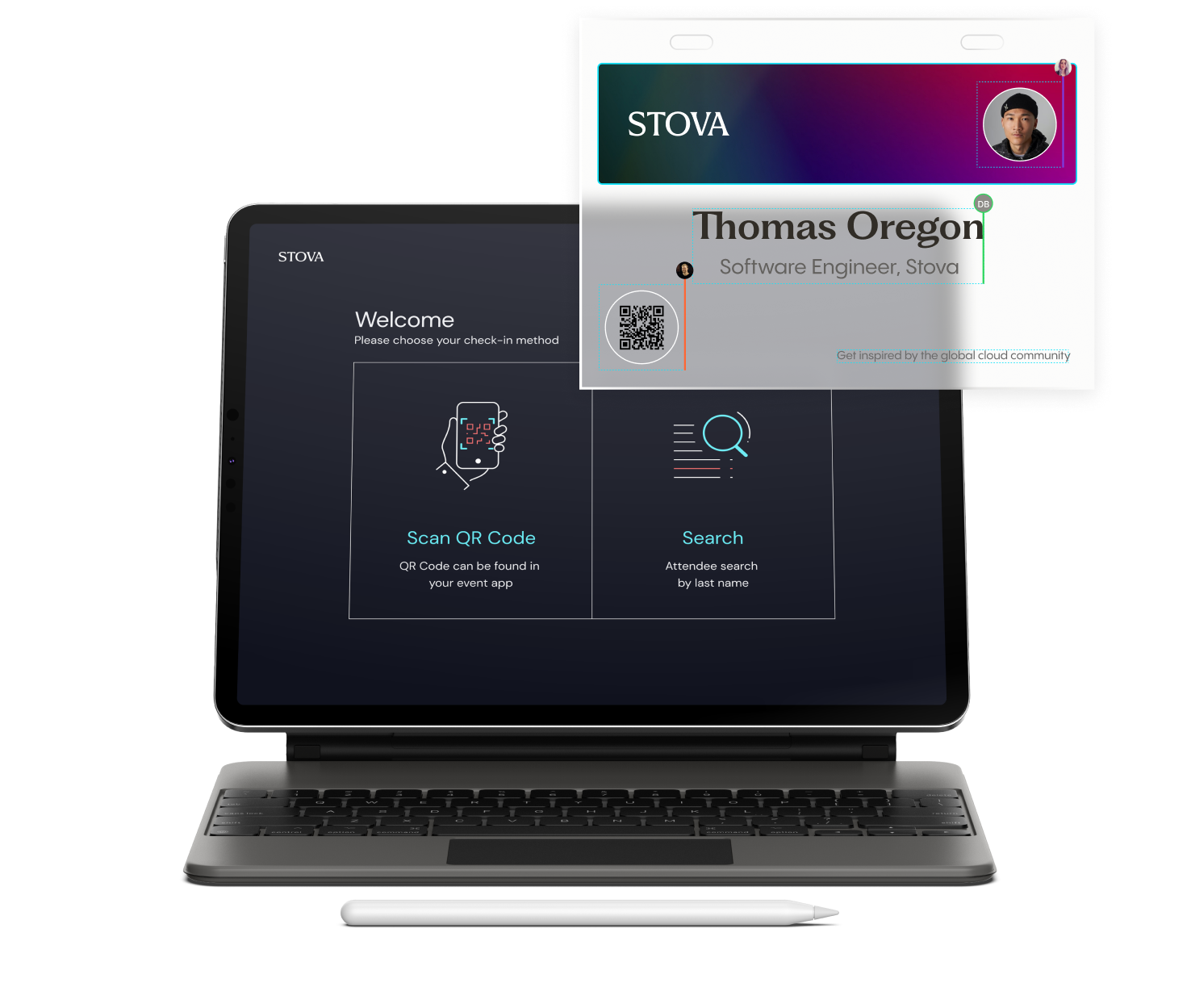
Create Connections with Custom Mobile Apps
Our various mobile applications are available on multiple devices and alleviate common event pains, such as materials distribution and attendee payment.
Create Safe Environments
Offer attendees a contactless way to access the show floor by utilizing a custom mobile app as your digital badge.
Notify and Inform Attendees
Keep your attendees informed in real-time with on-site guidance, session notifications, exhibitor information, and more.
Delight Sponsors and Exhibitors
Share app usage reporting with sponsors to see the ROI of their investment, and give the attendees the ability to connect and network with like-minded individuals.
Say Goodbye to Third Party Integrations
Information collected during the registration process is completely integrated into the event app, allowing you to focus on the event, not on data capture.
Real-time Tracking and Session Support
Manage, edit, and report on session data in a more streamlined manner utilizing your own iOS or Android devices, or using Stova’s software onsite. Scan leads using NFC, Bluetooth, UHF, QR codes, or business card capture.
Capture Qualified Leads, Seamlessly
Drive Revenue and engagement while delivering more ROI for your exhibitors and sponsors with touchless lead retrieval using the Stova Lead Retrieval App.
Eliminate Manual Workflows
Directly upload leads into any marketing automation systems.
Quality Leads As They Happen
Analyze leads in real-time by monitoring the lead dashboard in the exhibitor portal.
Track Data in Real Time with Session Support
Track session attendance in real-time and obtain insights into attendee behaviors. Session Dashboards give you a bird-eye-view of current attendee data, so you can pivot in the moment.
Support Your Onsite and Virtual Teams 24/7/365
Dedicated members of our managed services team are with you every step of the way, both onsite and virtually 24/7.
Partner with your Platform
Onsite support specialists are on standby to assist in any onsite technology issues that you may have, from session access control to badging & registration.
Train with the Experts
We help you make the most out of using any of Stova’s end-to-end solutions, by providing you and your team with dedicated, focused training.
Ready to learn more?
Whether your event is virtual, hybrid, or in-person, enhance your attendee’s journey with an event ecosystem built for your audience. Ready to walk through Stova's event technology solutions? Schedule some time with us today.